Essential 8 Services & Consulting
The Essential 8 strategies to mitigate cyber security incidents are designed to protect businesses from cyber security incidents and breaches. Achieve compliance and implement the strategies with eStorm's Essential 8 services & consulting
What is the Essential Eight?
The Essential 8 is a set of security strategies initiated by the Australian Signals Directorate (ASD). It provides the fundamental guidelines required to ensure you are implementing the correct IT security habits across your business. While no mitigation strategy is guaranteed to prevent cyberattacks, the Essential Eight strategies as a minimum will make it much more difficult for attackers to compromise your systems.
The two main goals of the Essential Eight are to:
1. Prevent attacks
2. Limit the extent of attacks
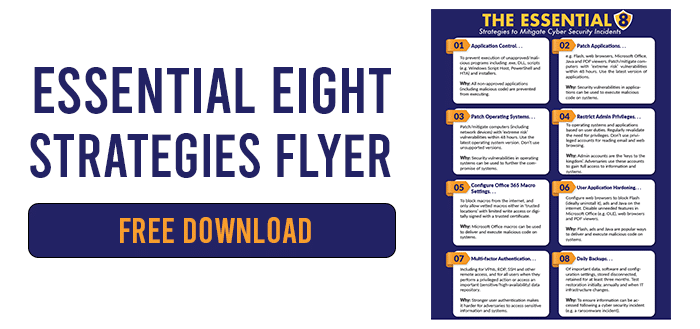
The Essential Eight Strategies
Prevent Attacks
Controlling the applications that can be downloaded and executed on your network prevents the spread and implementation of malicious code. The ASD recommends you ‘whitelist’ a set of pre-approved apps and prohibit applications that are not on this list from being installed.
Patching (or updating) applications regularly is an important part of keeping your IT software and systems secure from potential threats. Old/unsupported software create vulnerabilities in your network that can easily be taken advantage of. Ensure applications with ‘high risk’ vulnerabilities are patched within 48 hours and keep on top of updates for popular software such as Microsoft Office, Java and PDF viewers.
While most macros are used to automate regular tasks such as formatting documents, some can pose a security risk. Cyber attackers can program macros to run malicious code to spread viruses on your computer or network. Therefore, the ASD suggests you should only enable macros from trusted and verified sources and block those from unapproved or unreliable sites.
Ads, plugins and unneeded features on your applications are popular ways to execute malicious code on your network and systems. You should consider blocking ads and Java, and also disabling unnecessary features/plugins in Office, PDF views, web browsers and any other software you use regularly.
Limit the Extent of Attacks
The less admin accounts you have, the better. This is because cyber attackers actively seek to seize to admin accounts in order to gain greater access to your network. Set privileges according to user roles (e.g. someone who primarily uses their system for viewing emails and web browsing does not need admin access), and review those privileges regularly.
Implementing multi-factor authentication prevents adversaries from accessing your data and systems, even if they have a password. Setting up 2-or-3-step authentication processes (including passwords, biometrics and SMS confirmations) will limit the manoeuvrability of potential attackers if they gain access to your system.
As mentioned in Step 2, patching and updating your operating systems to latest versions (specifically to avoid unsupported versions) is critical in preventing vulnerabilities in your network. Patch ‘extreme risk’ vulnerabilities in computers/networks within 48 hours and install new updates as soon as feasibly possible.
In case of a cyber security incident or outage, you should ensure your data is protected by undertaking regular backup methods. Backup new data, software and configuration settings daily and retain for at least 3 months. You should also store two backup copies of your data on two different mediums (such as a cloud service and offline disk drive) and store one of these offsite (not on your own network). Read more about data protection here.
Using The Essential 8 framework, eStorm will implement a multi-layered defence strategy to combat the increasing number of cyber threats in today’s world so you can confidently focus on growing your business.
The Essential Eight Maturity Levels
In order to assist businesses and organisations with the implementation of the Essential Eight, three maturity levels have been defined for each mitigation strategy.

Maturity Level One
Partly aligned with the intent of the mitigation strategy

Maturity Level Two
Mostly aligned with the intent of the mitigation strategy

Maturity Level Three
Fully aligned with the intent of the mitigation strategy
Is your cyber security strategy compliant?
In just the past year, we've seen cyber security breaches on NSW Health, JBS Foods and the University of NSW. These breaches have cost millions of dollars to rectify. Can you afford the loss in revenue, trust, and clean-up costs?
We know the initial start up costs to get your cyber security strategy compliant can be daunting. That's why we're offering a FREE discussion/meeting with one of our cyber security experts. Our expert will sit down with you to discuss your current IT security strategy, what you should be focussing on, and whether you're taking the right steps towards compliance.
Completely free. No obligations to continue your cyber security journey with us.
Dedicated IT Security Consultants
Just like the system solutions we present to you, we are also able to deliver a support service model to suit your specific requirements. These include adhoc, prepaid or managed services.
We truly pride ourselves on bringing fast, friendly and effective expertise to your technology needs. Whether on-site, or via our service desk, our expert technicians combine their IT service and support expertise with friendly and welcoming service to deliver a superior customer experience.
If you need business IT security/cybersecurity services, let the team at eStorm help. Contact is today!
Related Articles
Best Practices for Backing Up Your Data
Cyber-crime and data loss are ever increasing in today’s technology-reliant society. The loss of important company data and client records […]
What are Software Audits?
What Is a Software Audit? A software audit is a formal review of an organisation’s software suite which can be […]
eStorm at EduTECH!
EduTECH is the largest Education event in Asia-Pac and the Southern Hemisphere, and eStorm were happy to be a part […]
Case Studies
Get business driven results with eStorm.

The internal IT Manager at Silky Oaks left with no notice and very little documentation. Silky Oaks approached eStorm to assist in keeping their systems operational while they assessed their ongoing IT requirements.
Lighthouse Christian School promoted their junior technician to a management role after the departure of their previous IT manager. The new manager felt he was still developing his IT knowledge and experience, and thus would not be able to single-handedly run the school’s IT. LCS then endeavoured to find a Managed Service Provider that could provide supplemental IT support and services.

To meet the needs of a large client, Liquid Animation worked with eStorm to architect a solution that allowed international animators to seamlessly access data. This was achieved using a combination of cloud-based work stations and Amazon Web Services.
Work better with eStorm
See why businesses all across Australia and NZ partner with eStorm Australia